Board Directors have fiduciary and regulatory responsibility for the organisations they serve. That now includes understanding and mitigating the cyber security threats and risks facing their organisations. Cyber resilience rests with the board, which must ensure they have the knowledge to perform this role. Cyber resilience requires UK Boards to be IT skilled. Boards should consider appointing an IT specialist as a NED, even if this means appointing someone who traditionally did not tick all the boxes.
The ever-increasing cyber risks UK organisations face
Around 40% of ethical hackers surveyed in 2022 by the SANS Institute said they could break into most environments they test, if not all. Nearly 60% said they need five hours or less to break into a corporate environment once they identify a weakness. What is scary here is that ethical hackers are restricted in the techniques they are permitted to use. Techniques used by criminals would significantly escalate the success rates and speed of attacks.
In a 12-month period, The UK Cyber Security Breaches Survey 2022 found
- 39% of UK businesses identified a cyber attack
- 21% of these businesses identified their attack as sophisticated
- 56% cited ransomware as a major threat and that they had a policy not to pay
31% of businesses and 26% of charities estimate they were attacked at least once a week - The average cost of cyber attacks is £19,400
COVID
IT and data are an integral part of an organisation, regardless of size and business model. For some, the adoption of new software, technology and business practices was expedited by COVID. Cash was replaced with digital transactions. Staff were forced to work from home, using personal devices and networks. Meetings, negotiations, and sales had to occur online rather than face-to-face. Organisations had no choice but to act and fast-track the adoption of new technologies, apps and software to survive. Most organisations lacked the time, resources and expertise to thoroughly evaluate these technologies and the potential risks.
Many organisations have been left vulnerable, seeing an increase in the number, sophistication and types of cyber attacks. Cyber resilience is almost unattainable for organisations that lack the funds and required technical expertise. Even with the pandemic dwindling, hybrid working models and newly adopted technologies are here to stay.
The 4th Industrial Revolution
The fourth industrial revolution, also known as the digital revolution, combines technological and human capacities in an unprecedented way through self-learning algorithms, self-driving cars, human-machine interconnection and big data. Increasingly, machines are making decisions with less and less intervention by human beings in this decision-making process, and the speed of their decision-making is rising. We are in the era of AI.
The invasion of Ukraine
The UK is yet to experience a cyber attack relating to the Russian invasion of Ukraine, but it is still viewed by the National Cyber Security Centre (NCSC) as a heightened threat, requesting UK organisations be prepared for an extended period.
The types of cyber risks UK organisations face
There are many cyber threats organisations are currently vulnerable to. Some are more damaging than others, particularly concerning immediate financial losses. Most have an effect on staff resources and potentially damage the organisation’s reputation.
#1 Email Fraud
No email protection system can be 100% failsafe. Yes, email fraud has been around for a long time; however, the strategies and sophistication only continue to grow. Often even those who consider themselves IT savvy are unable to identify them. There are numerous ways organisations can fall victim to email fraud; you could write a book on them. In general, staff can receive emails from criminals impersonating external parties they trust, or the criminals impersonate the organisations and defraud their trusted parties.
#2 Cloud data breaches
Since the pandemic and hybrid work began, organisations have had to move vast amounts of data and application services to cloud-based environments. Storing data in the cloud is not risk-free.
#3 Ransomware attacks
Ransomeware attacks can be devastating for any organisation. These attacks involve criminals gaining unauthorised access to encrypt, lock or delete target organisations’ systems. They then demand money to restore access or keep the attack confidential. An emerging practice in ransomware attacks is stealing an organisation’s data and then threatening to release the data to the public (usually on the dark web) unless a ransom is paid.
#4 Software supply chain attacks
Also known as a 3rd party attack, the hackers will access via an outside provider that has access to your system, usually via a software update or software platform provider. This type of attack has increased by 650%, with Gartner predicting that 45% of organisations globally will have a supply chain attack by 2025.
#5 Denial of services attacks
Attacks indented to affect the availability of an organisation’s network, systems or website. In June 2022, Cloudflare experienced the largest DoS attack in history.
#6 Malware attacks
Malware is often unintentionally downloaded or installed by those within the organisation’s network. The malicious software may destroy data, sabotage systems, or quietly capture sensitive information.
#7 insider attacks
An insider threat is someone within your organisation who jeopardises the integrity or availability of sensitive information. This may involve inadvertently leaking sensitive information, falling for a scam or misplacing a company device. However, insider attacks can be an intentional acts of stealing or sabotage.
#8 Phishing Emails
Criminals use bulk scam emails, messages or phone calls to trick victims. The aim is often to make you visit a website that may download a virus onto a computer or steal information.
Emerging Cyber Risks
Smishing
Untargeted scam SMS messages sent in bulk requesting personal information, call a number or click on a link.
Deepfake Attacks
Deepfake technology allows one to spoof or doctor a person’s video, making it convincingly seen as another person. In essence, the technology is now available for criminals to produce a fake video of an executive and use it to manipulate trusted parties. Or, the criminals could produce a fake video of an executive performing an illegal act, then blackmail them or the company not to release it.
Cyber Spying
The uptake of teleconferences and digital meeting software has seen a new threat of cyber spying, where unauthorised people or external parties gain access to sensitive corporate information by eavesdropping on live meetings or viewing recorded ones.
IoT
Internet of Things (IoT) – devices and objects connected to the internet, e.g. smart locks, sensors and cameras. Every IoT device will collect data, and most require 3rd party software. Where that data is saved will depend on the individual device and its task. Every IoT device will have access to some form of network. All leads to the vulnerability of hacking or spying.
Organisations NEED digitally smart boards
Organisations need to shift their focus from cyber security to cyber resilience. Cyber resilience incorporates the ability to prepare for, respond to and recover from cyber attacks. This is a strategic responsibility that must be instigated and driven by the board.
A strategic cyber resilience focus will see the board and organisation benefit by
- Reducing financial losses
- Meeting legal and regulatory data and privacy requirements
- Improve corporate culture and internal processes
- Protect brand and reputation
Cyber resilience requires UK Boards to be IT skilled. Not every board member needs to be a technical expert, but they need to know enough about cyber risks to discuss and plan for the needs of the organisations they represent. They need sufficient IT knowledge to converse with those who do.
At the board level, awareness and education must be a priority, as cyber risks will only continue to evolve and escalate. Boards and board members will be increasingly exposed, legally and reputational, if they are not making decisions to mitigate cyber risk and effectively communicate breaches to stakeholders.
Even with the rising rates of cyber attacks, most board UK members are confident they understand the threat landscape and have taken sufficient action to keep their organisations safe. The Cybersecurity: The 2022 Board Perspective Report found that in the UK, 85% of board members believe that their organisation has made adequate investments in cybersecurity and 82% that they were adequately prepared.
Unfortunately, many studies have found this not to be the case, with boards’ primary focus being the bottom line, still valuing technology as an operational process that improves business. Most boards lack the knowledge to foresee the true impact of a cyber failure. Even more, boards lack the skills and knowledge required to respond should a cyber incident occur.
The UK Cyber Security Breaches Survey 2022 found that
- only 54% of businesses have acted in the past 12 months to identify cyber security risks,
- only 19% of businesses have a formal cyber incident response plan,
- while 39% have assigned roles should an incident occur.
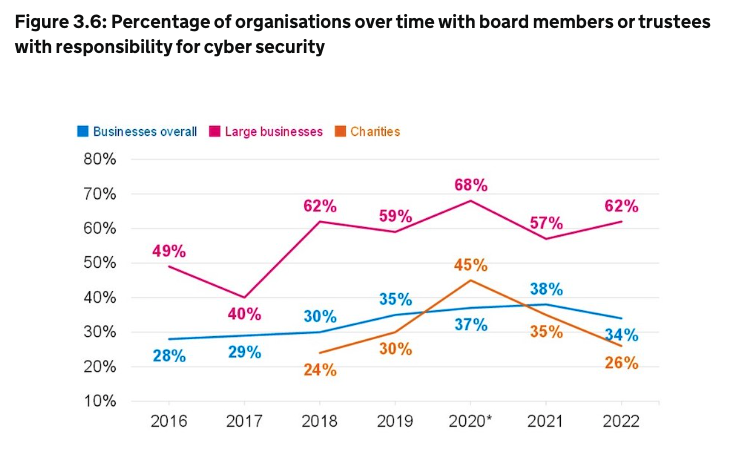
Boards need to be IT skilled
The UK Cyber Security Breaches Survey 2022 also found that limited board understanding meant that cyber risk was often passed on to; outsourced cyber providers, insurance companies, or an internal cyber colleague. They also found that only 34% of businesses and 26% of charities have board members or trustees accountable for cyber security as part of their job. This figure has barely changed since 2016, while the cyber risks have increased substantially
Cyber resilience requires UK Boards to be IT skilled. The lack of expertise at the board level will only result in a lack of funding and action for cyber resilience. Organisations should complete a board skill matrix to identify gaps in skills and competencies concerning cyber risk and IT knowledge. Depending on the result, they need to identify a board member to be responsible for cyber risks or appoint a new director who can either be internal (CIO or CTO) or external (non-executive director).
Boards looking to appoint a non-executive director need to prioritise IT and cyber skills over those previously seen as essential, including finance and governance experience. They should seek IT specialists who successfully implement large-scale technology projects and demonstrate strategic skills and capabilities. Previous board experience should not be a requirement. Technology moves fast, and boards can not afford to wait to find a board member who ticks all the traditional boxes.
Organisations also have the option to upskill the current board members. However, new skills are harder to learn with age. With the average board member between 50 and 70 years old, the complexity required to upskill cybersecurity and IT systems is daunting. For most boards, the best option is to appoint a board member with specialist IT skills.
What does this mean for those of you seeking Non-Executive Board Roles?
If you are an IT specialist, it’s time to sell yourself appropriately. When preparing your board pitch and board CV, ensure you articulate your IT skills and their value at the board level. Apply for board roles even if you don’t feel that you tick all the boxes. Your IT skills should, now more than ever, be of more value and supersede some of the more traditional requirements a chair looks for when appointing a new director.
If you are not an IT specialist, you should consider gaining and keeping up with IT knowledge, particularly in cyber security. The demand for non-executive directors who are IT specialists or have IT knowledge will undoubtedly increase. So, instead of investing your time and money in governance courses, consider courses and certifications in IT, risk management and cyber security.
Additional Resources & Articles
- NCSC UK – Cyber Security Tool Kit for Boards– Helping board members get to grips with cyber security
About the Author
David Schwarz is CEO & Founder of Board Appointments – The UK’s leading board advertising and non-executive career support firm. He has over a decade of experience in putting people on boards as an international headhunter and a non-executive recruiter and has interviewed over one thousand non-executives and placed hundreds into some of the most significant public, private and NFP roles in the world.

